About a year ago I published this post:
128. Encrypting your email, chat and VOIP in linux (Debian Wheezy)
While I'm using gajim for encrypted chatting on a daily basis, always sign my emails with PGP/GPG in thunderbird and evolution, and keep a
truecrypt container in my dropbox account, I've noticed that I don't ever use twinkle, which was the voice encryption solution I looked at in post 128.
The time is thus ripe to explore alternatives. Also, seahorse and evolution have changed enough that updated screenshots may be warranted. So here's Encryption for 2013. You will find that the most difficult thing about encryption is to convince other people to use it as well.
The tl;dr version is: use gajim. It's awesome.
--- Beginning of the boring bits ---
Why?
I'm not actually paranoid, but what about
*'If you don't have anything to hide, then what are you worrying about?' ? The issue with that kind of reasoning is that it can twisted into meaning that if you do worry, then you do have something to hide, and mere possession of will imply guilt. Presumably, if people in general are using e.g. PGP, the risk of it being banned or restricted (or being enforceable) is smaller. See e.g.
this if you're living in the US.
* What happens if you gmail account gets hacked? Could someone glean enough information from your conversations and email to steal your identity?
* Do you need to send someone your PIN, bank card info or SSN but don't necessarily feel
* Do you need to discuss something but keep it confidential?
* It's fun! Being able to encrypt gives you a bit of a power trip.
What does annoy me are people who think that they aren't targets because 'why would anyone want to hack me'? Low-profile individuals are rarely targets in their own right, but what about the company you are working for? What about friends of yours? What about the possibility of opportunistic drive-by hacking where targets aren't selected by who they are, but by lapses in security?
In my case, I work for a large university -- gaining access to the intranet for an outsider would only be the first step in potentially compromising thousands of computers or accessing the personal information of tens of thousands of people (has happened at every uni I've worked). I manage servers at two universities -- if they get compromised their access to high speed internet could be used for spam routing (has also happened).
I have friends who work with classified projects presumably involving nuclear weapons (nat'l lab in the US) -- I might be an intermediary target.
I have a credit card, and a credit history. What if someone steals my identity and takes out a loan in my name? (has happened)
Or what if I have confidential data on a USB stick and I lose it -- if it's encrypted damage control is a lot easier (has happened at my uni).
Again, I'm not really paranoid, but there is always a tiny risk that someone, for whatever reason, is targeting you.
OTR and GPG/PGP
Note that
I am NOT an expert on this. I've used PGP a lot, but have only recently been introduced to OTR. Also, merely being a user of something doesn't make an expert at it.
What I write might be wrong.
PGP (pretty good privacy)/
GPG (it's open sourced implementation) is a proven encryption method which uses asymmetric encryption with a private and a public key. You use someone else's public key to encrypt messages to them, and only their private key can decrypt it. Likewise, you give your public key to someone who wants to email you -- they use that to encrypt messages to you, and you -- and only you -- can decrypt it with your private key. PGP also supports signing to verify authorship -- you can sign (not encrypt) a message using your private key, and then anyone with your public key can decrypt it.
It's worth emphasizing this:
if you encrypt with your private key, anyone in the world can decrypt it.
Whenever you generate a new key pair, you can publish the public key on a range of online repositories, such as
http://pgp.mit.edu/ I think seahorse (gnome, evolution) and enigmail (thunderbird) can automatically search public key servers for public keys.
PGP is in principle a very strong encryption method using a 2048 byte (or larger) key. However, it suffers from a major drawback: anyone who can get their hands on your private key can decrypt everything. That basically means that anyone who gets access to your unencrypted harddrive can copy your key and eavesdrop. The longer you use the same key, the more likely it is that this will already have happened, especially if you have traveled through the US and been forced to give them access to your laptop. Leaving your laptop in your hotel room -- especially in a place like China (although it goes for anywhere) -- is probably also not advisable. Since you can't keep an eye on your hardware 24/7, this is a serious issue.
Another potential issue is that if you sign conversation with a key, then that conversation can be attributed to you i.e. a third, eavesdropping party may be able to ascertain who the conversing parties are.
Again, emphasis: your conversation may be safe now, but if in three months your key is lost all your conversations for years will be decrypted.
You can deal with this to some extent by either encrypting your entire harddrive, or by keeping your private key on an encrypted USB stick (be mindful of the increased risk of misplacing your usb stick and other people gaining access to it -- any encryption can generally be broken, given enough time and resources).
My main use of PGP/GPG is to have candid discussions via chat, and to sign my email.
OTR (Off the Record) is a 'new' (since 2004) alternative and is described in (accessible) detail here:
http://www.cypherpunks.ca/otr/otr-wpes.pdf
It aims to solve a lot of the issues with PGP by doing away with a long-lived key. It also aims to make it impossible for a third party to identify the conversing parties. From what I understand it works more or less like this:
If we decide to chat, I generate a key,and you generate a key. Once we're done talking, we dispose of the keys. No-one --- not even the conversing parties -- can decrypt the conversation, which also ensures that nothing will surface by accident at a later date. PGP can obviously be used in the same manner, but it's the implementation of it which has to be convenient. Obviously, in practice this works a whole lot better for chat than email.
Anyway, from my reading of it OTR works pretty much the same as PGP (using large primes and public/private keys) -- it's just the actual implementation which differs. On starting the chat you click on a button to generate your key pair, and the public key gets sent to your chat partner and vice versa. Exit the chat session and your keys are gone. OTR also uses authentication of messages to ensure authorship i.e. even though a man in the middle can encrypt messages to you using your public key and pretend that they are written by your conversation partner, the lack of the correct authentication signature will alert you to the fact that someone is spoofing the messages. PGP does the same by signing with the private key. There's no way to prove authorship based on the authentication signature though -- all you can do is determine that a series of messages came from the same author, but there's nothing which intrinsically proves who that person is. With PGP, on the other hand, if the assumption is that the private keys of the conversing parties have not been compromised, then they both are who they claim they are (of course you might've been duped into using someone else's public key and then all bets are off).
Anyway, OTR improves on PGP and works well for chat. PGP is probably still the easier solution for email.
SRTP (secure real-time transport protocol)
I don't know much about this, and am heavily relying on the Wikipedia page.
SRTP is an encryption method for streamed data, which I read to include voice and video. It needs a key management protocol, such as
ZRTP. The way keys are managed depend on the protocol. As far as I understand ZRTP uses temporary asymmetric keys which are exchanged at the beginning of the encryption part of the conversation, similar to OTR, but includes one major difference: a call begins with a verbal exchange of a specific value displayed in the clients of the two parties conversing. This is to avoid that there's a man in the middle attack -- you will presumably recognise the voice of the person you're talking to and be able to verify the identity that way.
I won't cover data encryption using e.g.
Truecrypt, in particular, since I've covered it in detail before, e.g. here:
http://verahill.blogspot.com.au/2012/04/using-truecrypt-with-dropbox.html
Solutions that I won't consider:
While e.g. skype uses encryption, you're not in control. Also, it's not open source, so who knows how it works
While you using https and google talk in a browser encrypts you video/voice calls and chat, you're not in control -- google can decrypt your conversation any time.
--- End of the boring bits ---
PGP/GPG keypair
The easiest way to do it is probably via the seahorse GUI.
sudo apt-get install gnupg seahorse
Start seahorse (known as Passwords and Keys in Gnome 3).
Once you've made a key pair, synchronise it with a server so that other people can get your public key, e.g.
Alternatively, you can do everything on the command line:
gpg --gen-key
gpg (GnuPG) 1.4.12; Copyright (C) 2012 Free Software Foundation, Inc.
[..]
Please select what kind of key you want:
(1) RSA and RSA (default)
(2) DSA and Elgamal
(3) DSA (sign only)
(4) RSA (sign only)
Your selection? 1
RSA keys may be between 1024 and 4096 bits long.
What keysize do you want? (2048)
Requested keysize is 2048 bits
Please specify how long the key should be valid.
0 = key does not expire
= key expires in n days
w = key expires in n weeks
m = key expires in n months
y = key expires in n years
Key is valid for? (0) 0
Key does not expire at all
Is this correct? (y/N) Y
You need a user ID to identify your key; the software constructs the user ID
from the Real Name, Comment and Email Address in this form:
"Heinrich Heine (Der Dichter) "
Real name: I Lindqvist
Email address: i.lindqvist@email.net
Comment: fake address
You selected this USER-ID:
"I Lindqvist (fake address) "
Change (N)ame, (C)omment, (E)mail or (O)kay/(Q)uit? O
You need a Passphrase to protect your secret key.
You'll get asked for a passphrase twice. Then:
We need to generate a lot of random bytes. It is a good idea to perform
some other action (type on the keyboard, move the mouse, utilize the
disks) during the prime generation; this gives the random number
generator a better chance to gain enough entropy.
Not enough random bytes available. Please do some other work to give
the OS a chance to collect more entropy! (Need 283 more bytes)
..+++++
...+++++
We need to generate a lot of random bytes. It is a good idea to perform
some other action (type on the keyboard, move the mouse, utilize the
disks) during the prime generation; this gives the random number
generator a better chance to gain enough entropy.
+++++
Not enough random bytes available. Please do some other work to give
the OS a chance to collect more entropy! (Need 109 more bytes)
.....................+++++
gpg: key 2B4C5636 marked as ultimately trusted
public and secret key created and signed.
gpg: checking the trustdb
gpg: 3 marginal(s) needed, 1 complete(s) needed, PGP trust model
gpg: depth: 0 valid: 1 signed: 0 trust: 0-, 0q, 0n, 0m, 0f, 1u
pub 2048R/2B4C5636 2012-05-02
Key fingerprint = 5B71 C3F1 0C2D E008 B299 21A8 019F 907E 2B4C 5636
uid I Lindqvist (fake address)
sub 2048R/78F9B6C1 2012-05-02
gpg --list-key
/home/me/.gnupg/pubring.gpg
-----------------------------
pub 2048R/2B4C5636 2012-05-02
uid I Lindqvist (fake address)
sub 2048R/78F9B6C1 2012-05-02
To add more email addresses, do
gpg --edit-key 2B4C5636
>adduid
and follow the prompts. You do not want to add subkeys.
Do
>trust
to set the trust level. Ultimate for your own key, full for your pals.
Implementation
Chat:
Gajim
Gajim supports both PGP (natively) and OTR (via a plug in). It's also easy to use and written in python, which is a plus.
To enable
PGP/GPG, go to Edit, Accounts, Personal Information, Choose Key:
You need to assign the public key to the contacts you want to chat with. First get the public key -- either from an online repo or by email from your contact. In e.g. seahorse, go to Remote, Find Remote Keys and search:
Then, in gajim, do
To
enable OTR, go to Edit, Plugins, click on the Available tab and wait a little while for the list to populate:
To
use OTR, do the following:
 |
| Start chat, click on the settings icon, select off-the-record, and start |
 |
| It's now encrypted |
 |
| To verify the identity of the other party, click on Authenticate contact |
 |
| Ask a question |
 |
| And the other person answers |
 |
| Authentication achieved |
Alternatives
mcabber also support PGP/GPG, and is a curses based program. See
here for configuration.
pidgin and
jitsi both support OTR, but not PGP.
Pidgin and mcabber are in the debian repos.
Email:
Evolution:
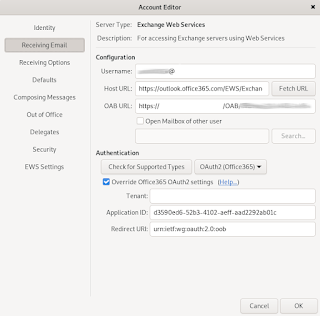
Enabling PGP/GPG is very easy -- edit your account, and go to the Security tab:
To encrypt, start a new message and click on Options. You might want to have html turned off.
Thunderbird:
You'll need to install enigmail.
You can select your key
etc. under key management.
Alternatives
Mutt does PGP/GPG and is a neat curses-based program.
Z/SRTP in Voice
There are a couple of solutions for 'secure' voice and video. I looked at Twinkle before, and while it's a capable SIP program, the downside is that it requires access to a SIP service (e.g. Ekiga, or via your ISP). What is really needed are clients which can encrypt communication going via e.g. google talk/jabber and the likes. Jitsi does that, and is open source.
I won't consider Skype for the usual reasons -- it's not free, open or transparent.
Jitsi
Get jitsi by doing
wget https://download.jitsi.org/jitsi/debian/jitsi_1.0-latest_amd64.deb
sudo dpkg -i jitsi_2.0-latest_amd64.deb
Start Jitsi and set up an account. You can add more accounts later by going to Options and clicking the Accounts tab.
Anyway, start Jitsi, and go to Options, Security to get an overview. Here's the ZRTP tab. Basically you CAN change the parameters, but you're advised not to:
Jitsi also does OTR chat:
And you can set a master password, so that people can't start jitsi if you leave your desktop unprotected.
You don't need to do anything to enable ZRTP as it will automatically be used if both your and your partner's clients support it, so here's OTR in Jitsi: